Update The default WPA2-PSK passphrase used in some Belkin routers simply replaces a character of the device’s MAC address with another hecxadecimal character, according to security blogger Jakob Lell.
Lell describes the situation as follows:

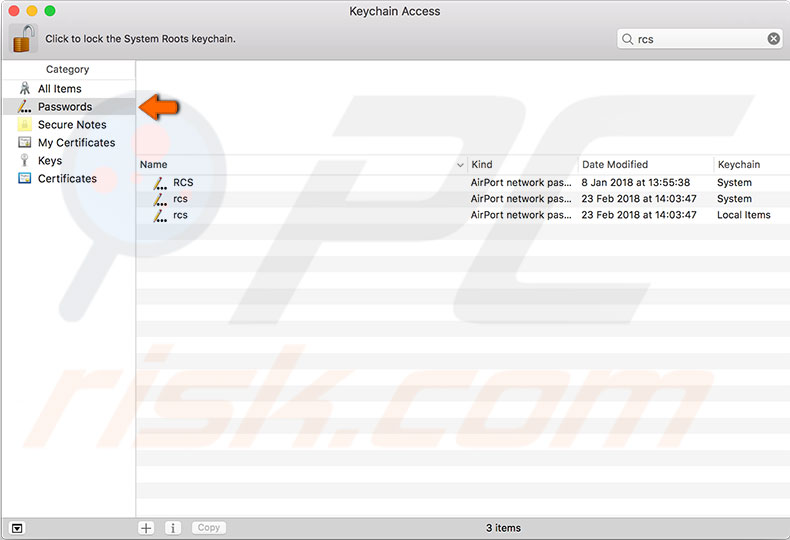
Keychain Access isn’t only useful to show Wi-Fi passwords on your Mac. It can also store your applications, internet and web form passwords. If password management is something you are not great at, consider looking into 1Password on the Mac App Store. It’s a very useful app! Method 2: Show a Wi-Fi password with Terminal. On macOS, revealing up a saved wifi password is simple. First, you can pull up Terminal and type in the following. Security find-generic-password -wa NAME OF YOUR WIFI NETWORK Same deal as. Netsh wlan show profile NETGEAR50 key=clear Under the security settings, in the ‘key content’, you see the WiFi password of that particular network. Besides knowing the Windows 10 WiFi password.
Each of the eight characters of the default passphrase are created by substituting a corresponding hex-digit of the WAN MAC address using a static substitution table. Since the WAN MAC address is the WLAN MAC address + one or two (depending on the model), a wireless attacker can easily guess the wan mac address of the device and thus calculate the default WPA2 passphrase.
In either case, that’s problematic because it is possible to interrogate WiFi routers in order to learn their MAC address. Some models even advertise the address on the case of the device!
Lell’s revelation, which he says makes it possible to deduce passwords by drawing up a simple substitution table, means all an attacker needs to do to compromise a device is learn its MAC address and then spend a few minutes converting it into Hex.
Lell’s post on the topic suggests Belkin’s Surf N150 Model F7D1301v1, N900 Model F9K1104v1 and N450 Model F9K1105V2 are all susceptible to the attack.
He also writes that other routers may have the same issue, with only the substitution table differing.
“It is likely that other Belkin devices are affected as well,” Lell’s post says, adding that he has tried to engage the company on the issue since January 2012, without success. “Unfortunately, Belkin has not yet cooperated with us to fix the vulnerability and/or confirm a list of other affected devices,” he says.

The good news is that users need only change the password to make the poorly-coded default codes irrelevant. And we all know users are always diligent about that kind of chore and would never leave a system in an insecure state.
Belkin has responded to The Register's inquiries, saying 'We have been made aware of the work recently published by two researchers at the Technische Universität Berlin regarding the default security configuration of Belkin routers, and appreciate their contribution to improved Wi-Fi security.'
The responses goes on to say the company is 'reviewing the details of the published research to understand its full implications' and will fix the problem if necessary, 'so as to ensure our users continue to benefit from the maximum level of security possible while also guaranteeing interoperability and ease of use.” ®
My Wifi Password On Mac
